After Strava, Polar is Revealing the Homes of Soldiers and Spies
Polar, a fitness app, is revealing the homes and lives of people exercising in secretive locations, such as intelligence agencies, military bases and airfields, nuclear weapons storage sites, and embassies around the world, a joint investigation of Bellingcat and Dutch journalism platform De Correspondent reveals.
In January Nathan Ruser discovered that the fitness app Strava revealed sensitive locations throughout the world as it tracked and published the exercises of individuals, including soldiers at secret (or, “secret”) military outposts. The discovery of those military sites made headlines globally, but Polar, which can feed into the Strava app, is revealing even more.
The manufacturing company known for making the world’s first wireless heart-rate monitor uses its site ‘Polar Flow’ as a social platform where users can share their runs. Compared to the similar services of Garmin and Strava, Polar publicizes more data per user in a more accessible way, with potentially disastrous results.

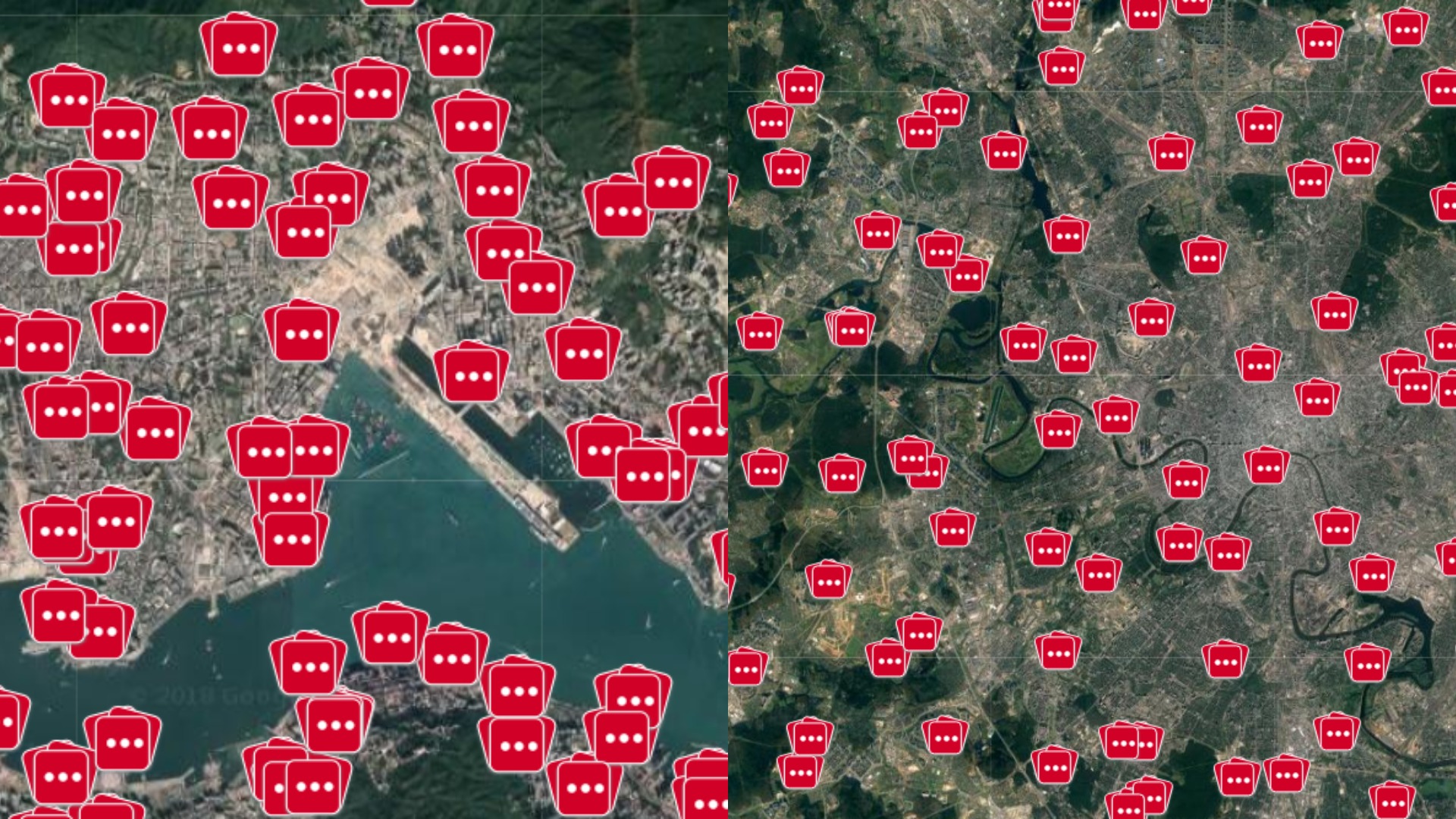
Exercises tracked at a military base in the Middle East. Red squares with white dots are clusters of many more sessions which started at that location.
Home is where the heart is
By showing all the sessions of an individual combined onto a single map, Polar is not only revealing the heart rates, routes, dates, time, duration, and pace of exercises carried out by individuals at military sites, but also revealing the same information from what are likely their homes as well. Tracing all of this information is very simple through the site: find a military base, select an exercise published there to identify the attached profile, and see where else this person has exercised. As people tend to turn their fitness trackers on/off when leaving or entering their homes, they unwittingly mark their houses on the map. Users often use their full names in their profiles, accompanied by a profile picture — even if they did not connect their Facebook profile to their Polar account.
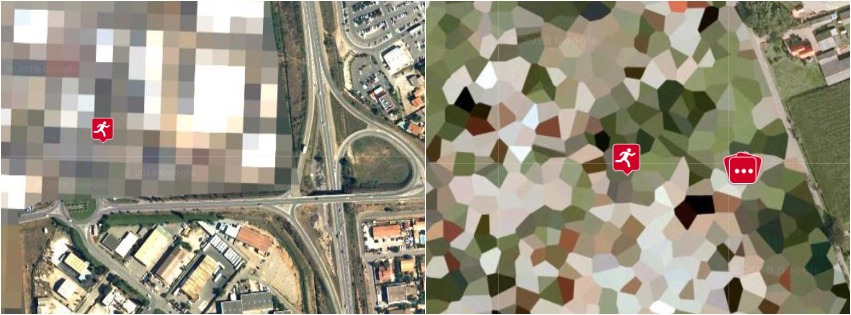
Secretive locations are blurred by Google on satellite imagery, but Polar reveals the individuals exercising there.
Polar is not the only app doing this, but the difference between it and other popular fitness platforms, such as Strava or Garmin, is that these other sites require you to navigate to a specific person to view separate instances of his or her sessions, each exercise having its own small map. Moreover, they often limit the number of exercises that can be viewed. Polar makes it far worse by showing all the exercises of an individual done since 2014, all over the world on a single map.
As a result, you only need to navigate to an interesting site, select one of the profiles exercising there, and you can get a full history of that individual.

Polar’s map based on individualized data, showing exercises done by one person in the Middle East, and the United States.

Recorded activities globally from the past 6 months. Left to right: Global, North Korea and South Korea, French Polynesia, Antarctica.
Know by heart
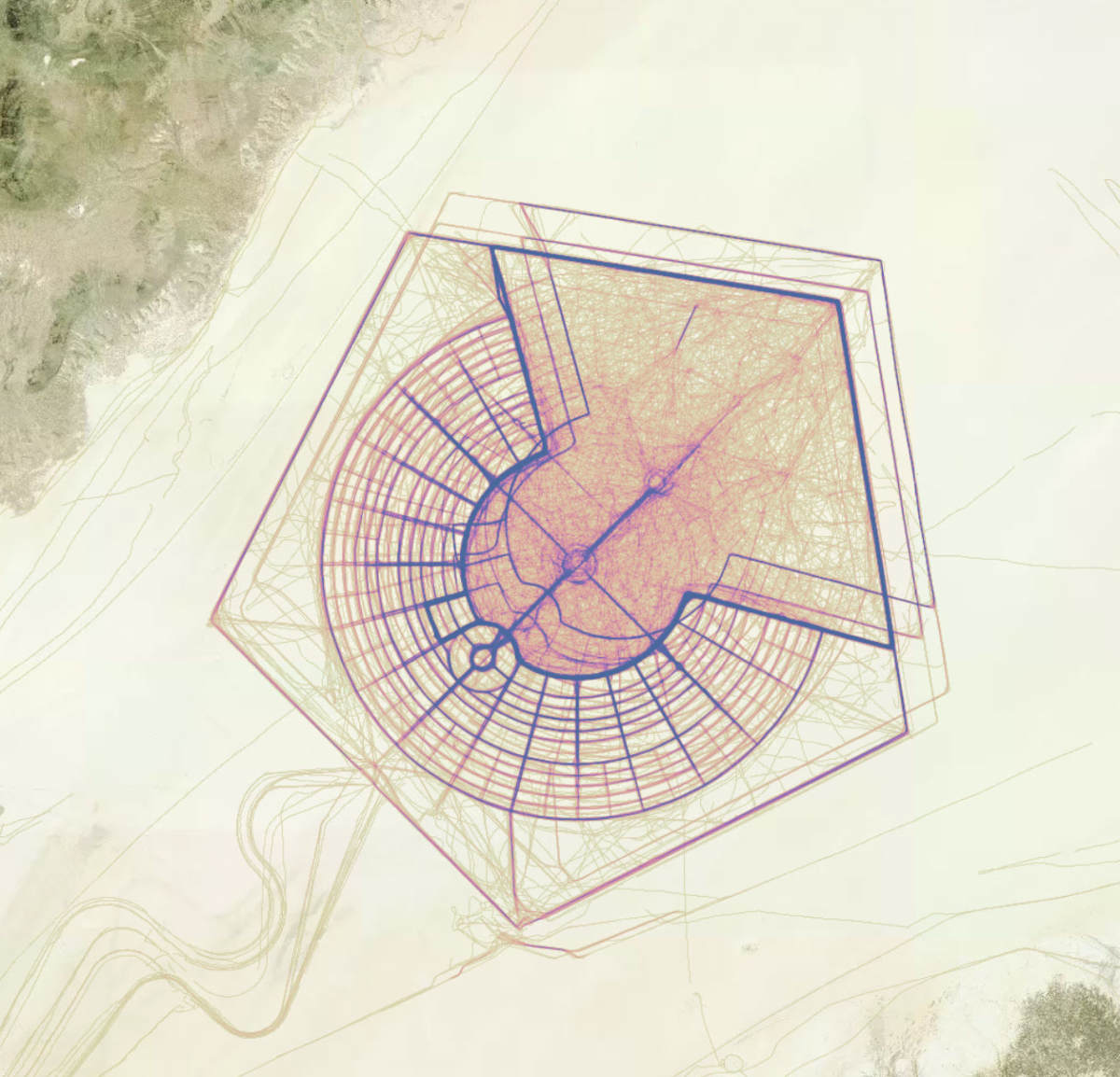
With only a few clicks, a high-ranking officer of an airbase known to host nuclear weapons can be found jogging across the compound in the morning. From a house not too far from that base, he started and finished many more runs on early Sunday mornings. His favorite path is through a forest, but sometimes he starts and ends at a car park further away. The profile shows his full name.
Activities normally shrouded in secrecy are laid bare with incredible detail. At a U.S. Air Force base where armed drones are stationed, an intelligence officer can be found exercising. Again, his name and profile picture openly available.
We can find Western military personnel in Afghanistan through the Polar site. Cross-checking one name and profile picture with social media confirmed one soldier or officer’s identity. Polar showed his runs in several military bases spread throughout the Middle East, as well as the start and finish of dozens of exercises from a house in New York state. In early 2017, as the Polar app freely tells us, he made a trip to the west-side of the US and used a bike there. He also logged exercise from a hotel during a stay in Thailand. All this activity was accompanied with a time-stamp, his exact route, his heart-rate, and the amount of calories he burned.
We can go through other military bases in the Middle East, Southern Asia, and Africa to find Western military servicemen and women and cross-reference their full names with social network profiles, including LinkedIn. A selection of individuals that we found on the Polar site who were identifiable from their public information, and whose homes we where able to locate includes:
- Military personnel exercising at bases known, or strongly suspected, to host nuclear weapons.
- Individuals exercising at intelligence agencies, as well as embassies, their homes, and other locations.
- Persons working at the FBI and NSA.
- Military personnel specialised in Cyber Security, IT, Missile Defence, Intelligence and other sensitive domains.
- Persons serving on submarines, exercising at a submarine bases.
- Individuals both from management and security working at nuclear power plants.
- A CEO of a manufacturing company, exercising in locations all over the world.
- Americans in the Green Zone in Baghdad.
- Russian soldiers in Crimea.
- Military personnel at Guantanamo Bay.
- Troops stationed near the North Korean border.
- Airmen involved in the battle against the Islamic State.
This list is not exhaustive. We were able to scrape Polar’s site (another security flaw) for individuals exercising at 200+ of such senstive sites, and we gathered a list of nearly 6,500 unique users. Together, these users had made over 650.000 exercises, marking the places they work, live, and go on vacation.
The security implications are obviously grave. In countries where soldiers were banned from wearing their uniforms on the street in the off-chance that they would run into a potential terrorist, addresses and living patterns can now be found easily by anyone with internet access and the wits to use Polar’s site. In its current form, it is not difficult to find the time of deployment, home, photograph, and the function of a soldier in a conflict zone. It does not take much imagination to see how this information could be used in dangerous ways by extremists or state intelligence services. This is especially concerning considering the data we managed to gather on personnel at multiple nuclear weapons storage sites.
The risk from Polar’s open data set also poses a risk to civilians, as those with ill intentions could use Polar to see when, and for how long, users in an area tend to be away from their homes, as well as when they are abroad if they bring the heart rate sensors with them.
Open Season
On registering your account, Polar asks you to provide a name, location, height, weight, date of birth, gender and the amount of training per week. Though you can obviously fill in fake information, the majority of users we surveyed provided what seems to be reliable information. Along with the ability to connect your account to Facebook, Polar also offers integration with five other apps (including Strava) to share “all your sessions automatically”.
Even with turning up the privacy settings, plenty of data will still be available. Here are some examples:
- Changing the privacy from ‘Public’ to ‘Followers’ will still let profiles show a name, photo and the location they wrote in during registering to anyone. Users would also need to turn off the option that allows others to become a ‘Follower’ automatically if they want to.
- Changing the privacy of sessions, even to the most strict, only affects new sessions. Older sessions will remain visible.
- Other fitness sites, such as Strava, provide the option to automatically prevent your home or work-location from being published. Polar doesn’t.
- It is possible to remove individual sessions, but many accounts appear to have hundreds of sessions logged, making it a very cumbersome process.
- There are sessions on the map which are completely private, not linked to anything else. However, once several of these private exercises starting and ending at the same home are located, it is still possible to gather information about when and where a person living there is going.
- User ID’s connected to “private” runs are easily retrievable, meaning it is still possible to connect exercises at different locations to one person.
The privacy policy has been updated in August 2017, and new accounts do have their default settings set to the most private options available, meaning users have to opt-in to share. In response to our research, Polar stated it recognized the sensitive nature of the data that was being revealed, and decided to temporarily suspend the ‘explore’ function. Polar is also now working on other solutions to these issues, such as adding the ability to remove the exercise history in one go.
Drawbacks
As with most open sources, Polar’s platform has its limitations. The Polar data relies on GPS, which can be inaccurate and spoofed, as Bellingcat described in an article on how to use Strava data. Moreover, users can (and probably should) turn their sensors on/off some distance from their homes. However, this is mostly negated by the fact that after multiple exercises, start- and end-points usually do average out to one particular residence.
The data tends to be accurate enough to tell when users are on the street, or on the property of a particular house. It becomes more difficult when dealing with dense cities and apartment buildings, though most fitness trackers seem to track elevation fairly accurately. In one instance, we tracked an individual working at a senstive location back to an appartment building. This person often started running in front of the building on the ground, but also had occasionally started an exercise at a much higher altitude. The difference between those two heights, combined with the coordinates, matched an exact floor within the apartment building.
The Heart of the Matter
Finding the names and even addresses of soldiers online is in itself not new. The amount of data people are (unknowingly) putting online has long raised concerns with both the public and with governments. Separate social media accounts, posts, and information can be pieced together to provide a fairly complete picture about an individual. As seen in hundreds of articles on Bellingcat and other open source-focused sites, images and videos reveal a lot of information and can be used in geolocation to provide additional context. What is new is how easy it has become to track individuals using fitness apps such as Strava, and especially with the scale and speed of Polar.
The U.S. military has already reviewed its rules for fitness trackers, and it is likely other countries will have done so too. However, it was still possible to identify plenty of American users at many military locations. It is also worth noting that this is only data from Polar heart rate monitors, while there is a whole world of tracking devices and apps out there. Chinese fitness apps, for example, are already used by hundreds of millions and are sponsored by the government, which aims to develop ”a variety of fitness activities and special sports items”.
Fitness devices and apps are just one more area where people need to be aware of what kind of data they are sharing, particularly as they strongly rely on sensitive data such as location and health-metrics. As always, check your app-permissions, try to anonymize your online presence, and, if you still insist on tracking your activities, start and end sessions in a public space, not at your front door. Finally, if you want absolute assurance that you are not running into data-pitfalls during future exercises, you could leave your device at home, so you can jog around anonymously to your heart’s content.
Foeke Postma (@FoekePostma) is a researcher on peace and security. He works at PAX, where he specializes in humanitarian disarmament.
The author would like to thank Aric Toler (@AricToler) for editing and feedback, as well as Wim Zwijnenburg (@wammezz) for his help.
The articles on De Correspondent:
Main story
Methodology
How we dealt with this sensitive data
Tips for fitness-tracker users